Deadbolt Defense Password Software
Platform™ and “Defending Your Privacy” are trademarks of Rune. Quired for your own personal use of the Software in accordance with this Agreement; or (c). 2 Locate and select the appropriate Deadbolt icon on your device. 3 Double Click the removable media containing. On a Windows system.

Chances are you or someone you know has been burglarized in their own home. Federal Bureau of Investigation (FBI) reported that in 2012 alone more than 2 billion burglaries occurred, and nearly 75% of these were in residential homes.
Even more chilling, 60% of burglaries were due to forcible entry. While burglars can sometimes find easy access through unsecured doors and windows, most don’t let locks or chain locks get in their way — they simply kick the door in. It’s easier than you might think. Very few things are as unsettling as not feeling safe in your own home. Installing a home security system can be a major deterrent to burglars, but there are even more precautions you can take to keep intruders out and give you the peace of mind you deserve. The best first defense is stopping burglars in their tracks with door security devices that are relatively easy to install and won’t break your budget.
How to Reinforce a Door Many residential exterior doors, particularly in older homes, have inadequate security hardware. Check your hardware to make sure each door is up to par. Your first priority? High quality deadbolt locks are a must on all exterior doors, doorknob locks alone are an open invitation to intruders (check out our article to see our highest rated locks). Make sure you replace each old lock with a grade 1 or grade 2 solid metal deadbolt lock with a throw bolt (the bolt that comes out of the door) no shorter than one inch (2.5 cm) in length. Then replace thin, lower quality strike plates with heavy duty, high quality strike plates (the metal plate in the frame that the throw bolt enters). The best strike plates should be secured with four metal screws that are at least three inches long. Be sure to to reinforce the door fully and effectively.
Unfortunately, even the best deadbolt locks and strike plates won’t keep out a determined intruder if your home entry doors, frames, jambs and hinges are weak. There are a number of door reinforcement devices on the market that can add some serious security against break-ins.
These devices include heavy-duty metal plates that fortify your jambs, hinges and frames, easy, do-it-yourself, screw-in plates that come in a variety of metal types and thicknesses. We’ve reviewed dozens of door security devices on the market, and hands down, EZ Armor is the best. This armor kit is among the best available and is recommended by police and independent testers as the safest door reinforcement for your home. While this product does require some installation, consumer reviews overwhelmingly indicate that it’s easy to install. There are a number of DIY videos online to help guide you through installation.
The manufacturer of EZ Armor, Armor Concepts, offers a number of combination kits, have a MSRP of $70 per pack and include door shields, jamb shields and hinge shields. Their mini combo pack is about $20 less and protects the jamb and lock area – the first two weak points to break when a door is kicked in. Check out this local news segment to see how EZ Armor stands up to a real test! Additional Tips for Door Security • Make sure you have solid wood or metal doors instead of hollow core models, which are simply cardboard surrounded by veneer. • Replace windowed exterior doors (paned French doors, half-window doors) with windowless doors. It’s all too easy for a burglar to break through the glass and unlock your door from the inside. • Add sturdy storm doors with good locking devices to your entries.
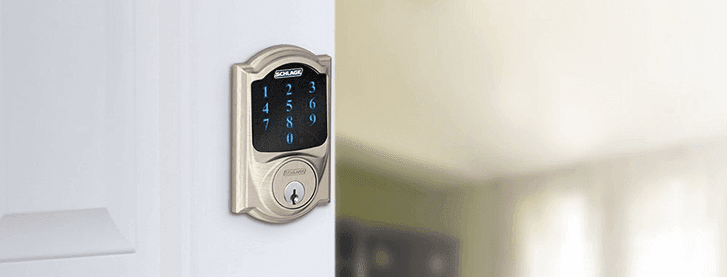
Storm doors add one extra layer of protection from intruders. • Install high security locks, including keyless passcode and fingerprint locks. • Add outdoor lighting at or near all outside doorways.
Track lighting on the sides and rear of your home close to entry doors can help deter break-ins. FBI reports show that in one-third of all home invasions, burglars enter through the front door, and they don’t wait for nightfall — 65% of home burglaries occur between the hours of 6 am and 6 pm. While it may cost you a little time and money, securing your front and other entry doors is one of the best ways to keep intruders out.
What door security solutions have you found to be most safe, affordable and easy to install? Have any door jammer installation tips? Tell us what products you love (or hate).
Kimberly has been writing for ASecureLife.com since 2013. She is passionate about home security and enjoys learning about the advances in home security and the trend of moving toward more of a do-it-yourself method. She is also an advocate for online safety and strongly believes in the power of strong passwords and identity theft protection for living a more secure life. Since purchasing her first home in 2016, Kimberly has been implementing everything she has learned through her writing at ASecureLife.com in her personal life and home. • • • Related Articles. “Spam” *Kimberly Kurimski* Content Manager, Cover Story Media®, Inc. *www.CoverStoryMedia.com * Like us on *Facebook * Follow us on *Twitter * ————————————————— *This transmission is intended only for use by the intended recipient(s).
If you are not an intended recipient you should not read, disclose, copy, circulate or in any other way use the information contained in this transmission. The information contained in this transmission may be confidential and/or privileged. If you have received this transmission in error, please notify the sender immediately and delete this transmission including any attachments. Cover Story Media℠, Inc. Does not guarantee the integrity of any e-mails or attached files. Cover Story Media℠, Inc. Fraternal Order Of Eagles Officer Handbook Quote. Does not warrant that any attachments are free from viruses or other defects.
You assume all liability for any loss, damage or other consequences which may arise from opening or using the attachments.*.
Using truly secure passwords: 6 essential reads • By Jeff Inglis • Sep 19, 2017 This was first posted to The Conversation. It is a roundup of articles previously published on The Conversation. Passwords are everywhere -- and they present an impossible puzzle. Social media profiles, financial records, personal correspondence and vital work documents are all protected by passwords. To keep all that information safe, the rules sound simple: Passwords need to be long, different for every site, easy to remember, hard to guess and never written down. But we’re only human!
What is to be done about our need for secure passwords? Get good advice Sadly, much of the password advice people have been given over the past decade-plus is wrong, and in part that’s because the targeting you specifically, write five scholars who are part of the Carnegie Mellon University passwords research group.
“People who are trying to break into online accounts don’t just sit down at a computer and make a few guesses. [C]omputer programs let them make millions or billions of guesses in just a few hours. [So] users need to go beyond choosing passwords that are hard for a human to guess: Passwords need to be difficult for a computer to figure out.” To help, those researchers have developed a system that checks passwords as users create them, and offers immediate advice about how to make each password stronger. Use a password manager All that computing power can too, writes Elon University computer scientist Megan Squire: “The average internet user has 19 different passwords. It’s easy to see why people write them down on sticky notes or just click the ‘I forgot my password’ link. Software can help!
The job of password management software is to take care of generating and remembering unique, hard-to-crack passwords for each website and application.” That sounds like a good start. Getting emoji into the act Then again, it might be even better not to use any regular characters., writes Florian Schaub, an assistant professor of information and of electrical engineering and computer science at the University of Michigan: “We found that emoji passcodes consisting of six randomly selected emojis were hardest to steal over a user’s shoulder. Other types of passcodes, such as four or six emojis in a pattern, or four or six numeric digits, were easier to observe and recall correctly.” Still, emoji are -- like letters and numbers -- drawn from a finite library of options. So they’re vulnerable to being guessed by powerful computers. Drawing toward a solution To add even more potential variation to the mix, consider making a quick doodle-like drawing to serve as a password. Janne Lindqvist from Rutgers University calls that sort of motion a “gesture” and is to do just that: “We have explored the potential for people to use doodles instead of passwords on several websites. It appeared to be no more difficult to remember multiple gestures than it is to recall different passwords for each site.
In fact, it was faster: Logging in with a gesture took two to six seconds less time than doing so with a text password. It’s faster to generate a gesture than a password, too: People spent 42 percent less time generating gesture credentials than people we studied who had to make up new passwords. We also found that people could successfully enter gestures without spending as much attention on them as they had to with text passwords.” Easier to make, faster to enter, and not any more difficult to remember? That’s progress. A world without passwords Any type of password is inherently vulnerable, though, because it is an, writes literature scholar Brian Lennon of Pennsylvania State University: “[E]ven the strongest password can be used anywhere and at any time once it has been separated from its assigned user.
It is for this reason that both security professionals and knowledgeable users have been calling for the abandonment of password security altogether.” What would be left then? Only attributes about who we are as living beings. Directv Installer Tool List. The unknowable password Identifying people based not on what they know, but rather their actual biology, is perhaps the ultimate goal. This goes well beyond fingerprints and retina scans, Elon’s Squire explains: “[A] computer game similar to ‘Guitar Hero’ [can] train the subconscious brain to learn a series of keystrokes. When a musician memorizes how to play a piece of music, she doesn’t need to think about each note or sequence.
It becomes an ingrained, trained reaction usable as a password but nearly impossible even for the musician to spell out note by note, or for the user to disclose letter by letter.”.